HTTP/3 is the successor to HTTP/2. Given that it took 16 years to move from HTTP/1.1 to HTTP/2, should you tackle the theme of HTTP/3?
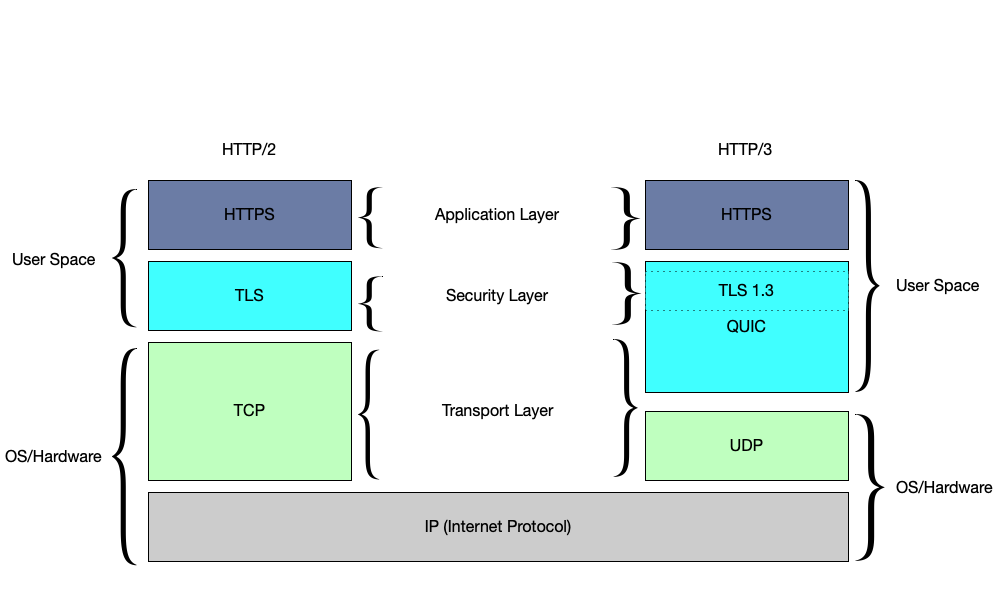
You probably guess so. I wouldn’t be writing about it if I didn’t think otherwise. It is worth keeping up to date on this thread. Just as HTTP/2 has made significant changes over HTTP/1.1 by switching from ASCII to the binary way of transferring data, HTTP/3 again makes significant changes, this time switching the underlying transport from TCP to UDP. This change is a key change that occurs in this iteration of changes.
Although HTTP/3 is still under development. The official specification is a sketch. It is slowly being implemented. Unfortunately, until then, you have to take into account the unstable operation of this version of HTTP/3.
However, there are many unknowns and questions about how HTTP/3 works. What are the Benefits? What should network engineers, system administrators, and programmers know?
Comparison between HTTP/2 and HTTP/3
HTTP/2 provides a big performance boost as it solves the HTTP row header blocking (HOL) problem. It implements request/response multiplexing, binary framing, header compression, stream prioritization, and server push.
The HTTP/3 protocol is even faster as it includes all of the HTTP/2 protocol and solves the TCP HOL blocking problem. HTTP/3 is still only a draft. It is more efficient, uses fewer resources (system and network), requires encryption (SSL certificates are mandatory) and uses UDP.
Web browsers will likely continue to support older versions of HTTP for a while. The performance benefits and search engine ranking of sites that support HTTP/3 will speed up large-scale implementation.
In the near future, website owners will likely want to support HTTP/3 as well. However, it is more controversial than HTTP/2, and may have natural opponents in the form of large networks.
Performance
A 100-millisecond delay in loading a web page can cut your conversion rate by 7%!
Source: Akamai Online Retail Performance Report: Milliseconds Are Critical
Read more: Best Web Hosting 2022 Reddit Recommendations
Is HTTP / 3 protocol already available?
While the standard is still in development, website owners and visitors can start getting HTTP/3 support through browsers, operating systems, and other client applications. Of course, there will probably be more changes to the standard, which has already undergone several implementations.
After the release of HTTP/3, the whole network won’t switch over right away. Many sites don’t use HTTP/2 yet.
One potential obstacle to the new protocol is that it requires increased CPU utilization by both the server and client. This impact is likely to decrease over time as technology develop.
TCP HOL blocking problem
TCP congestion control is supported by implemented mechanisms of packet rollback and retransmission. This is done by being used when data integrity loss is detected. Retransmission ensures that the data is ultimately delivered in a consistent and complete form.
Solving the TCP HOL problem
Solving the TCP HOL blocking problem required more than just switching to UDP, as it is still necessary to guarantee correct and complete data transfer while guaranteeing low server loads. The QUIC protocol was designed to improve the performance of this area, Provides optimized HTTP over UDP communication.
Since QUIC takes control of the management of streams, binary frames, etc., little remains to be done for HTTP/2. Defacto QUIC + HTTP is now HTTP/3.
The QUIC OSI model is based on the fact that the IP address is the base connecting the two stacks. The left HTTP protocol stack adds TCP, TLS, and HTTP / 2 to the IP address. The HTTP protocol stack on the right adds UDP, a special block, and “HTTP over QUIC”. The special block includes QUIC congestion control and similar to TCP and the ability to recover lost data and additionally a block of QUIC encoding / cryptography.
There are many versions of QUIC as the protocol has been developed and implemented in production environments for years. There is even a Google-specific version called GQUIC. Therefore, it is important to distinguish the old QUIC protocols from the new HTTP/3 standard.
What is UDP?
The User Datagram Protocol (UDP) is an alternative to TCP. It does not provide stream virtualization or the same guarantees that TCP offers. Instead, it provides an easy way to pack data into a packet, address it to another computer, and send it. It is unreliable, disordered, and has no form of congestion and loss control.
Its aim is to operate lightly and to provide the minimum operating functions necessary to enable communication. In this way, the application can exercise its own guarantees. This is often very useful in real-time applications. For example, in telephone calls, users typically prefer to receive 90% of the data immediately rather than 100% of the data ultimately.
Is HTTP/3 always encrypted?
HTTP/3 Includes Encryption One of the main implementation challenges for HTTP/3 is the need to modify the TLS / SSL libraries to add the required new functionality.
This change is due to the fact that HTTP/3 differs from HTTPS in terms of the encryption method. With the older HTTPS protocol, only the data itself is TLS protected, leaving the rest of the data decoded. In HTTP/3, both data and the transport protocol are protected. The protocol optimizes the redundant activities present in HTTP/2. Therefore, encrypting the transport protocol as well as the data actually increases the protocol performance.
Summary
The new protocol is faster and extends the currently used one. Nevertheless, I do not think it is quickly spread and available as the main one. I’m curious when WordPress hosting plans come with HTTP/3 as standard.